Introduction
Mobile applications today rely heavily on authentication layers such as access tokens, refresh tokens, API keys, and session identifiers to control and secure data access. For developers and data engineers, understanding how to handle authentication and tokens in mobile app scraping is essential to ensure uninterrupted and reliable data extraction. Without proper handling, issues like session expiry, failed requests, and blocked access can severely impact data pipelines.
Modern solutions such as a Mobile App Scraping API simplify this process by automating authentication workflows and maintaining secure token management. These tools help replicate real-user behavior, manage token refresh cycles, and reduce the complexity of interacting with protected APIs.
As mobile ecosystems evolve, authentication mechanisms are becoming more sophisticated, incorporating encryption, dynamic tokens, and multi-step verification. This makes it critical to adopt structured strategies for managing tokens efficiently. In this blog, we explore practical techniques, industry trends, and scalable solutions to overcome authentication challenges and build robust mobile app scraping systems.
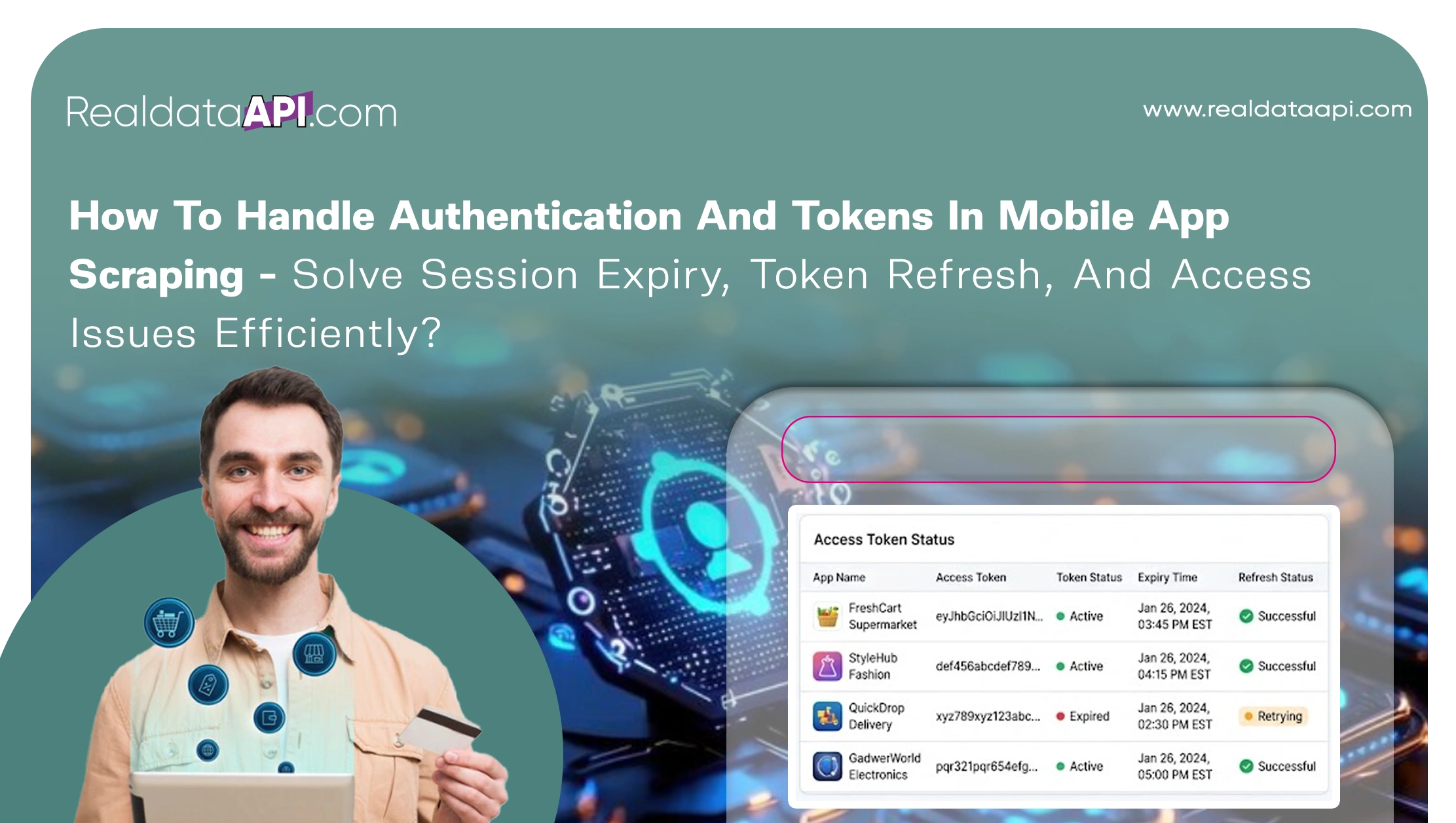
Ensuring Seamless Token Lifecycle Management
Efficient token lifecycle management is the backbone of any successful scraping system. By focusing on managing API tokens for mobile data extraction, businesses can maintain consistent access to protected endpoints without interruptions.
From 2020 to 2026, token-based authentication adoption has increased significantly, with over 80% of mobile APIs now relying on dynamic tokens. These tokens often have short lifespans, requiring automated refresh mechanisms to maintain access.
| Year | Token-Based Authentication Usage | Average Token Lifespan |
|---|---|---|
| 2020 | 55% | 60 minutes |
| 2022 | 68% | 45 minutes |
| 2024 | 75% | 30 minutes |
| 2026 | 82% | 15–30 minutes |
Automating token refresh workflows ensures that expired tokens are replaced without manual intervention. This involves detecting expiration timestamps, triggering refresh API calls, and securely storing new tokens.
Additionally, implementing token rotation strategies helps mimic real-user activity and reduces the risk of detection. Monitoring token usage patterns also allows systems to identify anomalies and prevent access failures.
By maintaining a structured token lifecycle, organizations can reduce downtime, improve reliability, and ensure seamless data extraction even in highly dynamic environments.
Overcoming Authentication Barriers in Mobile Environments
Authentication barriers are one of the most common challenges in mobile app scraping. Successfully handling login authentication in app scraping requires a deep understanding of how mobile apps validate users and sessions.
Between 2020 and 2026, multi-factor authentication (MFA) and encrypted login flows have become standard, increasing the complexity of scraping authenticated data. Approximately 65% of mobile apps now use advanced authentication techniques, including OAuth and JWT-based systems.
| Authentication Type | Adoption Rate (2026) | Complexity Level |
|---|---|---|
| Basic Token | 20% | Low |
| OAuth 2.0 | 45% | Medium |
| JWT-Based Auth | 35% | High |
To overcome these barriers, scraping systems must replicate the login process accurately. This includes handling headers, cookies, device fingerprints, and session IDs. Tools that simulate real-device behavior can significantly improve success rates.
Another key strategy is session persistence, which allows systems to reuse valid sessions instead of repeatedly logging in. This reduces server load and minimizes the risk of detection.
By understanding authentication workflows and implementing robust handling mechanisms, businesses can ensure reliable access to mobile app data while maintaining compliance with platform policies.
Accessing Protected Data with Precision
Accessing protected endpoints is a critical step in mobile app scraping. By extracting authenticated data from mobile apps, organizations can unlock valuable insights that are not available through public interfaces.
From 2020 to 2026, the volume of authenticated data has grown by over 70%, driven by the increasing reliance on personalized and secure APIs. This data includes user-specific content, pricing details, and real-time updates.
| Data Type | Availability Without Auth | Availability With Auth |
|---|---|---|
| Basic Listings | High | High |
| Pricing Data | Medium | High |
| User Preferences | Low | High |
| Real-Time Updates | Low | High |
To extract this data effectively, systems must include authentication tokens in API requests and maintain valid sessions. Proper header management and request sequencing are essential to avoid triggering security mechanisms.
Additionally, monitoring API responses helps identify changes in authentication requirements and ensures timely adjustments. This proactive approach minimizes disruptions and maintains data consistency.
By focusing on authenticated data extraction, businesses can gain deeper insights and build more comprehensive datasets for analysis and decision-making.
Building Secure and Scalable Authentication Strategies
Developing secure and scalable strategies is essential for long-term success. Implementing best practices for API authentication in scraping ensures that systems remain efficient, reliable, and compliant.
Between 2020 and 2026, organizations adopting structured authentication practices have reported a 50% reduction in access failures and a 40% improvement in data reliability.
| Practice | Benefit |
|---|---|
| Token Encryption | Enhanced security |
| Automated Refresh | Reduced downtime |
| Rate Limit Management | Avoid blocking |
| Session Monitoring | Improved stability |
Key best practices include encrypting tokens during storage, using secure communication protocols, and implementing retry mechanisms for failed requests. Additionally, respecting API rate limits and usage policies helps maintain long-term access.
Scalability can be achieved by distributing authentication tasks across multiple nodes and using centralized token management systems. This ensures that large-scale operations remain efficient and resilient.
By adopting these practices, businesses can build robust authentication frameworks that support continuous and secure data extraction.
Enhancing Efficiency with Advanced API Tools
Advanced tools play a crucial role in simplifying authentication and data extraction. Leveraging a Web Scraping API allows businesses to automate complex processes and improve efficiency.
From 2020 to 2026, the adoption of API-based scraping tools has increased by 58%, driven by their ability to handle authentication, token rotation, and request management seamlessly.
| Feature | Advantage |
|---|---|
| Token Automation | Reduced manual effort |
| Request Handling | Improved success rate |
| CAPTCHA Bypass | Enhanced accessibility |
| Geo-Targeting | Region-specific data access |
These tools also provide built-in mechanisms for handling authentication challenges, reducing the need for custom development. This allows teams to focus on data analysis rather than infrastructure management.
By integrating advanced API tools, organizations can streamline their workflows and achieve higher efficiency in mobile app scraping operations.
Scaling Operations for Enterprise-Level Data Extraction
As data needs grow, scaling becomes a critical factor. Implementing Enterprise Web Crawling solutions enables organizations to handle large-scale data extraction while maintaining performance and reliability.
Between 2020 and 2026, enterprise-level scraping adoption has grown by 72%, driven by the need for comprehensive data insights across multiple platforms.
| Capability | Impact |
|---|---|
| Distributed Crawling | High scalability |
| Centralized Control | Simplified management |
| Real-Time Processing | Faster insights |
| Multi-Platform Support | Broader data coverage |
Enterprise solutions often include advanced authentication management systems that handle token distribution, session tracking, and error recovery. This ensures uninterrupted operations even under high demand.
Additionally, AI-driven optimization techniques help improve efficiency and reduce resource consumption. By leveraging these capabilities, businesses can scale their data extraction processes without compromising quality.
This approach is essential for organizations aiming to stay competitive in data-driven industries.
Why Choose Real Data API?
Real Data API offers comprehensive Web Scraping Services designed to address the complexities of mobile app scraping. With expertise in how to handle authentication and tokens in mobile app scraping, the platform provides reliable solutions for managing tokens, handling authentication workflows, and ensuring secure data access.
Its advanced infrastructure supports automation, scalability, and compliance, making it suitable for both small-scale and enterprise-level projects. By offering end-to-end services—from data extraction to processing—Real Data API enables businesses to focus on insights rather than technical challenges.
With a strong emphasis on reliability and efficiency, Real Data API ensures that your data pipelines remain stable and effective in dynamic environments.
Conclusion
Mastering how to handle authentication and tokens in mobile app scraping is essential for building reliable and scalable data extraction systems. By implementing structured strategies, automating token management, and leveraging advanced tools, businesses can overcome challenges such as session expiry and access issues.
As mobile ecosystems continue to evolve, adopting innovative approaches to authentication handling will be key to maintaining consistent data access and gaining competitive insights.
Ready to build secure and scalable scraping solutions? Partner with Real Data API today and unlock seamless access to mobile app data with confidence!













